There were certain networks that were more prone to abuse, so looking for traffic into those hot spot networks was potentially a good indicator of abuse underway, said Lever, the first author of the paper and a student in Georgia Tech’s School of Electrical and Computer Engineering. You see a lot of DNS requests pointing to hot spots of abuse, that should raise concerns about potential infections.
The researchers also found that requests for dynamic DNS also related to bad activity, as these often correlate with services used by bad actors because they provide free domain registrations and the ability to add quickly add domains.
The researchers had hoped that the registration of previously expired domain names might provide a warning of impending attacks. But Lever found there was often a lag of months between when expired domains were re-registered and attacks from them began.
The research required development of a filtering system to separate benign network traffic from malicious traffic in the ISP data. The researchers also conducted what they believe is the largest malware classification effort to date to differentiate the malicious software from potentially unwanted programs (PUPs). To study similarities, they assigned the malware to specific families.
By studying malware-related network traffic seen by the ISPs prior to detection of the malware, the researchers were able to determine that malware signals were present weeks and even months before new malicious software was found. Relating that to human health, Antonakakis compares the network signals to the fever or general feeling of malaise that often precedes identification of the microorganism responsible for an infection.
You know you are sick when you have a fever, before you know exactly what’s causing it, he said. The first thing the adversary does is set up a presence on the internet, and that first signal can indicate an infection. We should try to observe that symptom first on the network because if we wait to see the malware sample, we are almost certainly allowing a major infection to develop.
In all, the researchers found more than 300,000 malware domains that were active for at least two weeks before the corresponding malware samples were identified and analyzed.
But as with human health, detecting a change indicating infection requires knowledge of the baseline activity, he said. Network administrators must have information about normal network traffic so they can detect the abnormalities that may signal a developing attack. While many aspects of an attack can be hidden, malware must always communicate back to those who sent it.
“If you have the ability to detect traffic in a network, regardless of how the malware may have gotten in, the action of communicating through the network will be observable,†Antonakais said. “Network administrators should minimize the unknowns in their networks and classify their appropriate communications as much as possible so they can see the bad activity when it happens.
Antonakakis and Lever hope their study will lead to development of new strategies for defending computer networks.
The choke point is the network traffic, and that’s where this battle should be fought, said Antonakakis. This study provides a fundamental observation of how the next generation of defense mechanisms should be designed. As more complicated attacks come into being, we will have to become smarter at detecting them earlier.
Read more in Chaz Lever, et al., A Lustrum of Malware Network Communication: Evolution and Insights, 38th IEEE Security and Privacy Symposium (22-24 May 2017)


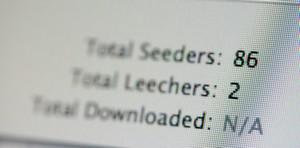 Spikes in traffic could indicate malware // Source: theconversation.com
Spikes in traffic could indicate malware // Source: theconversation.com